N3uron ensures the security of your data across critical infrastructures with a reinforced, end-to-end protection model that spans from plant floor to enterprise systems.
N3uron ensures the security of your data across critical infrastructures with a reinforced, end-to-end protection model that spans from plant floor to enterprise systems.
N3uron is built with security at its core. Its architecture follows industry-grade protection standards designed for IIoT environments, ensuring your systems are secure from the moment you deploy it.
Secure every connection with trusted encryption for data moving across nodes, services, and user interfaces.
Make access safer and easier to govern with strong authentication and granular permissions for every user.
Connect OT, DMZ, and IT securely while keeping networks isolated and limiting exposure.
Encryption
Secure every connection with trusted encryption for data moving across nodes, services, and user interfaces.
Authentication
Make access safer and easier to govern with strong authentication and granular permissions for every user.
Segmentation
Connect OT, DMZ, and IT securely while keeping networks isolated and limiting exposure.
N3uron is designed for distributed architectures, keeping connectivity simple and protected. N3uron Links combine outbound-only communications with the latest TLS encryption and a built-in Store & Forward mechanism, ensuring both data privacy and reliable delivery even during network interruptions. By leveraging trusted standards like MQTT and Sparkplug, N3uron ensures seamless integration with any modern IIoT deployment, while cryptographically secure digital certificates provide robust authentication for all node-to-node interactions.
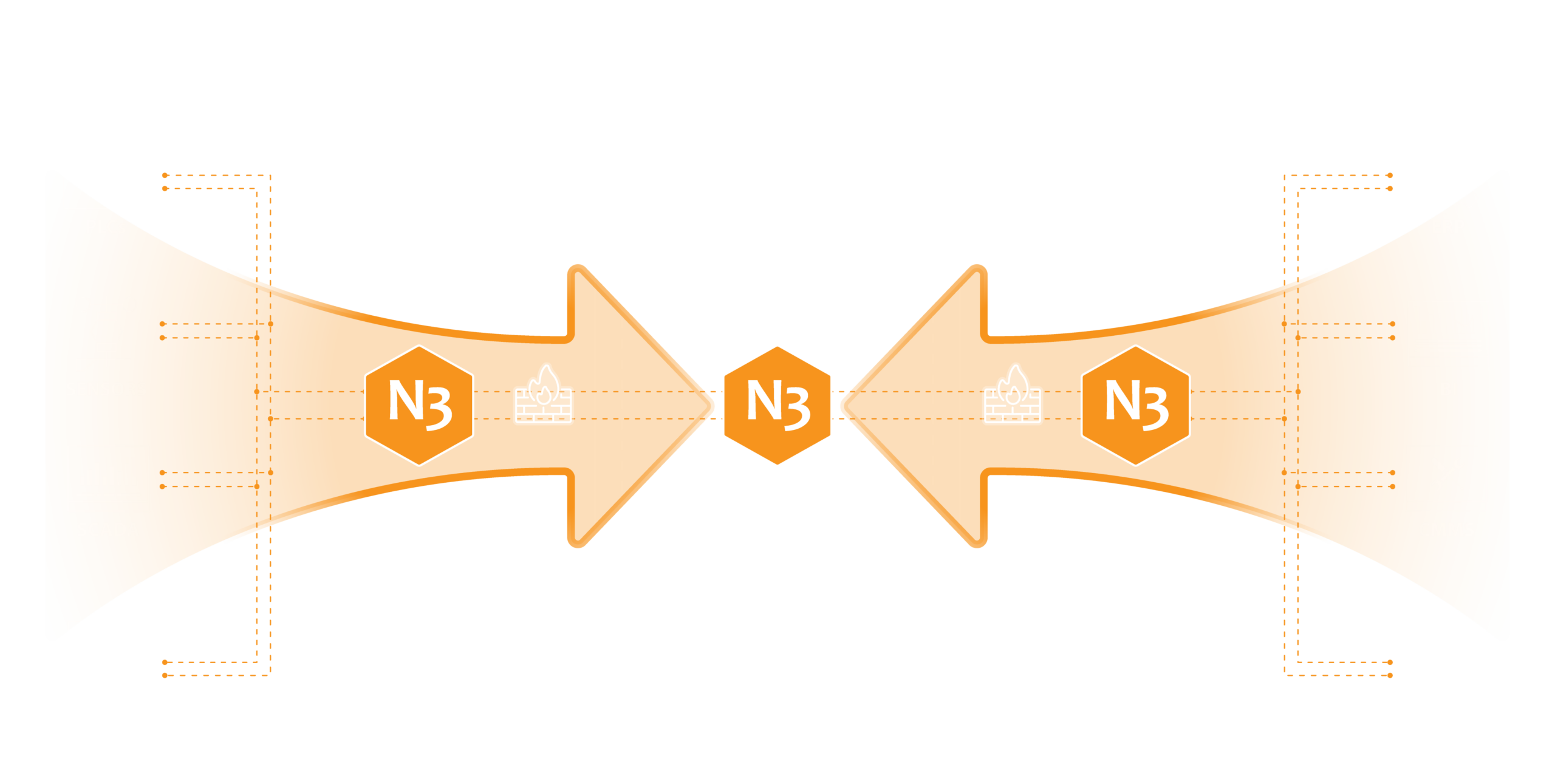
N3uron Links make it easy to securely connect OT and IT through a DMZ. With outbound-only connections from OT and IT, they help keep critical networks segmented, simplify firewall configuration, reduce exposed surface, and enable secure, bidirectional, controlled data exchange.
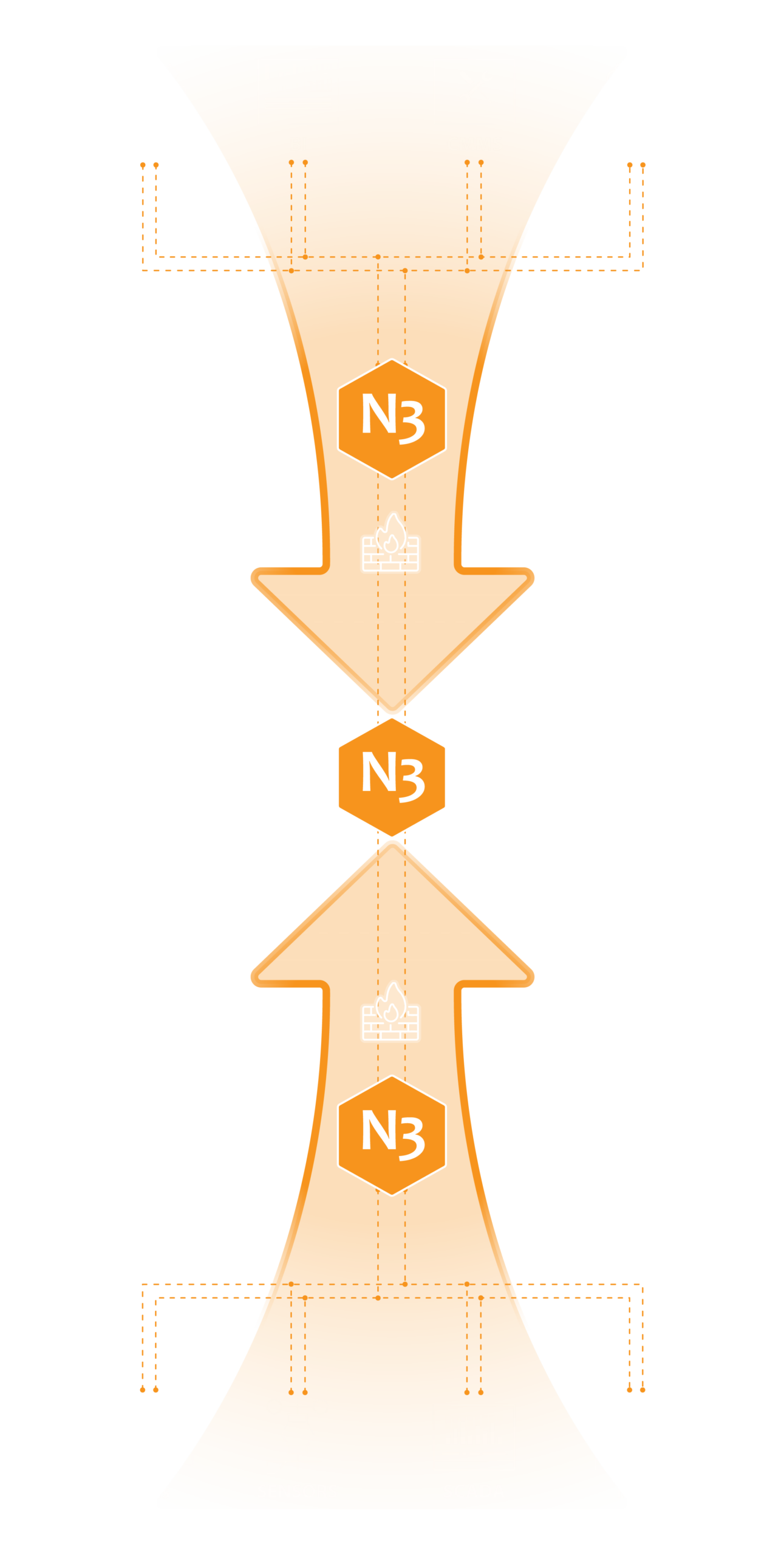
Data Diode One-Way Data Transfer
N3uron enables secure, one-way data transfer from OT to IT using Data Diode technology. Information can flow out, but never back in, providing strong isolation for critical assets.

Supply Chain Security
N3uron is digitally signed to guarantee the authenticity and integrity of the software, helping prevent supply chain attacks.
The N3uron WebUI should remain shielded from the public Internet and restricted to approved corporate access. For remote operations, Fleet Manager provides a simple, secure, and firewall-friendly way to manage N3uron nodes globally, without exposing them to the public Internet or relying on complex VPN setups.
Two-Factor Authentication
Lightweight Directory Access Protocol
N3uron uses a role-based access model that lets you manage permissions in a clear and centralized way. Users can be assigned one or multiple roles, and each role defines the level of access granted across the platform.
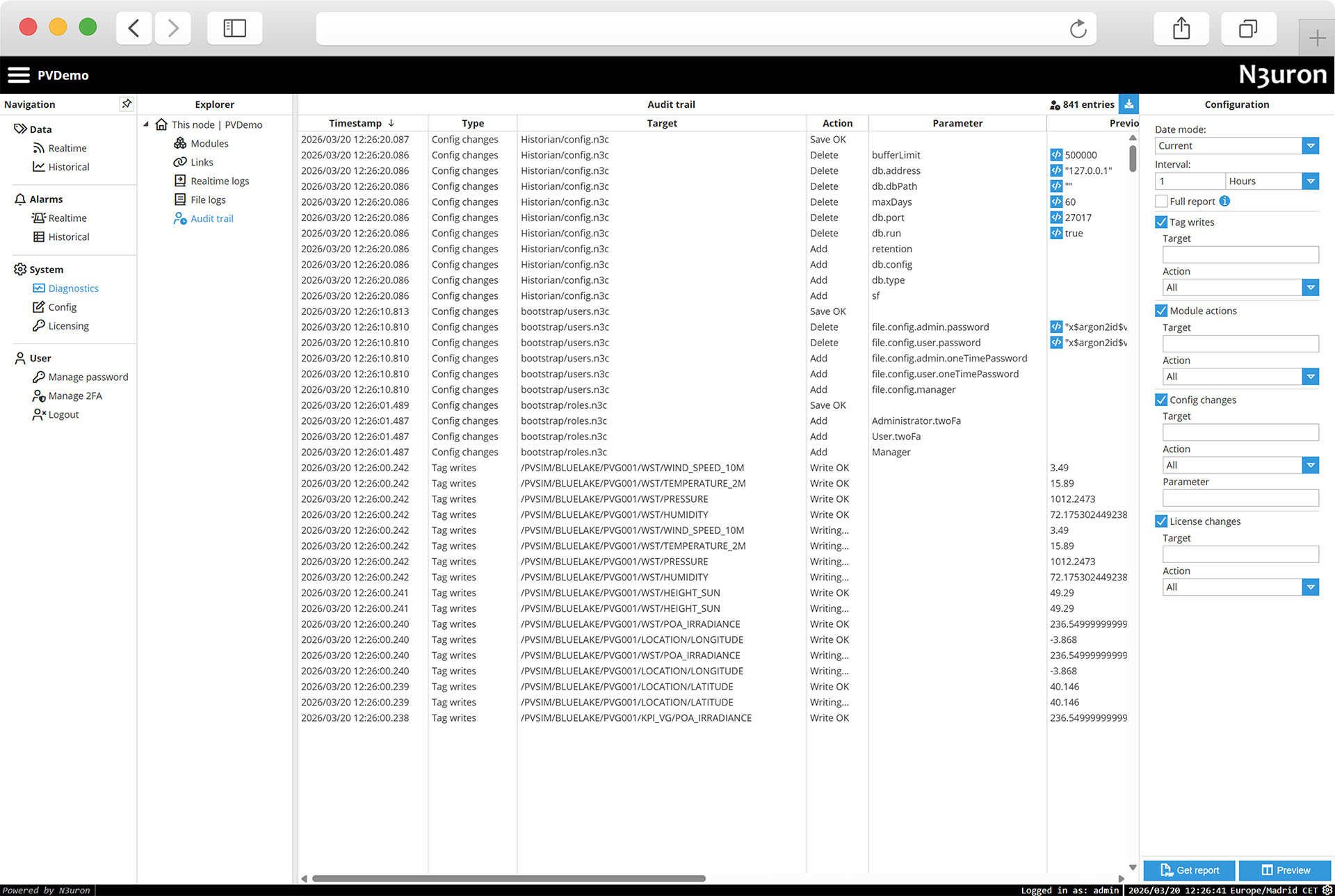
N3uron combines detailed logging with built-in audit trail capabilities to strengthen visibility, traceability, and compliance. Each module includes its own log file, with adjustable retention and log levels, and logs are stored in a plain-text format for easy forwarding to external SIEM tools on Linux and Windows. The Audit Trail module complements this by recording user and system actions, helping teams maintain accountability and accelerate incident investigation.
Logging & Audit Trail
N3uron provides detailed logging and auditing capabilities to help you monitor system activity and integrate with your existing security and compliance processes. Each module includes its own log file, with adjustable retention and log levels so you can control how much information is stored. Logs use a plain-text format for easy forwarding to external SIEM tools on both Linux and Windows installations.
N3uron’s broad protocol support, edge processing capabilities, and robust security model made it the clear choice to serve as the foundation of this company-wide initiative.
Kris Zawada, VP of Data Engineering at CES
N3uron’s broad protocol support, edge processing capabilities, and robust security model made it the clear choice to serve as the foundation of this company-wide initiative.
Kris Zawada,
VP of Data Engineering at CES

Encrypted Data
Protect data in transit with TLS-encrypted communications.
Outbound-Only Links
Enable secure node-to-node communication without opening inbound firewall ports.
Encrypted Data
Protect data in transit with TLS-encrypted communications.
Outbound-Only Links
Enable secure node-to-node communication without opening inbound firewall ports.
Data Diode Integration
Support secure unidirectional data transfer across segmented networks.
Role-Based Access
Control permissions with granular access by user, role, module, or tag group.
Identity & LDAP
Centralize user management through LDAP and Active Directory integration.
Two-Factor Authentication
Strengthen user access with built-in two-factor authentication and TOTP support.
DMZ Segmentation
Deploy secure architectures with controlled data exchange across DMZ zones.
Audit & Logging
Ensure full traceability with detailed system logs and user audit trails.
MQTT & Sparkplug
Enable secure interoperability through open industrial communication standards.
Trusted Engineering
Built with security-focused development practices aligned with OWASP guidelines.
Data Diode Integration
Support secure unidirectional data transfer across segmented networks.
Role-Based Access
Control permissions with granular access by user, role, module, or tag group.
Identity & LDAP
Centralize user management through LDAP and Active Directory integration.
Two-Factor Authentication
Strengthen user access with built-in two-factor authentication and TOTP support.
DMZ Segmentation
Deploy secure architectures with controlled data exchange across DMZ zones.
Audit & Logging
Ensure full traceability with detailed system logs and user audit trails.
MQTT & Sparkplug
Enable secure interoperability through open industrial communication standards.
Secure Engineering
Built with security-focused development practices aligned with OWASP guidelines.
Trust in a platform begins with trust in the team behind it. At N3uron, we follow rigorous security practices to protect our software, our operations, and the customers who rely on us every day. From how we develop and test our code to how we secure our own systems, we apply the same standards we recommend for industrial environments around the world. N3uron is also NIS2 compliant, reinforcing the reliability of our internal security processes.
Your data matters. Your operations matter. So security is built into everything we do.

Not all communications can be encrypted because many industrial protocols simply do not support encryption. However:
For protocols that do not natively support encryption (common in OT environments), N3uron provides secure alternatives, such as N3uron Links or MQTTS, to ensure safe transport across insecure network segments.
No. When using N3uron Links, all connections are outbound-only, and no open ports are required at remote facilities. This significantly reduces the exposed surface area in OT and industrial environments.
Yes. N3uron Links are designed for segmented architectures, allowing controlled bidirectional data exchange while keeping OT and IT isolated. The DMZ acts as a secure buffer and enforces strict boundaries between network segments.
Absolutely. N3uron is built for distributed and scalable architectures. Whether you deploy N3uron Links, MQTT, or Sparkplug, the platform keeps connectivity simple, encrypted, and resilient, even when the connection is unstable or interrupted.
No. N3uron includes a Store & Forward mechanism that preserves data during network interruptions and forwards it automatically once the connection is restored.
N3uron supports modern authentication practices including local user management, integration with Active Directory using LDAP and two-factor authentication (2FA) using Time-based one-time passwords (TOTP) compatible with any standard authenticator app.
Yes. Permissions are managed through a role-based access model. Users can have one or more roles, and AD Groups map directly to N3uron roles for streamlined, centralized control of access rights.
Yes. N3uron provides detailed logging and auditing across every module. Logs use plain-text formats that can be forwarded easily to external SIEM tools on Linux and Windows deployments.
Yes. N3uron enables secure, one-way OT-to-IT data transfer using Data Diode technology. Data can flow out of the OT environment but never return, eliminating inbound attack vectors.
Security is part of N3uron’s culture. The team applies rigorous security standards in software development, testing, infrastructure management, and operations, mirroring the same best practices recommended to industrial customers.
N3uron is also NIS2 compliant, reinforcing the reliability of our internal security processes.
Try N3uron’s free demo for yourself!
Full-featured demo mode (two-hour demo)
Some companies who have trusted in N3uron
N3uron software is an Industrial Edge Platform for IIoT and DataOps that streamlines the flow of data between industrial systems and business applications, either on-premise or in the cloud. N3uron provides an out-of-the-box solution for data standardization, normalization and contextualization, seamless integration with industrial and IT systems, efficient information management, and unparalleled scalability and security. The N3uron platform makes it easier for operations teams to aggregate, manage and analyze industrial data, resulting in enhanced productivity and informed decision-making. Whether you're looking to optimize your operations, reduce downtime or improve product quality, the N3uron platform is the answer.
CONTRIBUTING MEMBER
N3uron is a Contributing Member of the Eclipse Foundation, actively participating in the development of their robust ecosystem. By leveraging EF technologies, we offer innovative products and services that drive our corporate strategy forward. N3uron is Sparkplug Compatible Software.


DLMS® UA MEMBER
N3uron is a member of the DLMS® User Association, the global community that drives standardization in the energy and water industry. Being part of the DLMS UA represents N3uron's commitment to advancing smart metering and energy management solutions.
FOLLOW US
N3uron Connectivity Systems • Paseo de la Castellana, 91, 4º, 1; Madrid, 28046, Spain • +34 911 841 938 • [email protected]
N3uron software is an Industrial Edge Platform for IIoT and DataOps that streamlines the flow of data between industrial systems and business applications, either on-premise or in the cloud. N3uron provides an out-of-the-box solution for data standardization, normalization and contextualization, seamless integration with industrial and IT systems, efficient information management, and unparalleled scalability and security. The N3uron platform makes it easier for operations teams to aggregate, manage and analyze industrial data, resulting in enhanced productivity and informed decision-making. Whether you're looking to optimize your operations, reduce downtime or improve product quality, the N3uron platform is the answer.
CONTRIBUTING MEMBER
N3uron is a Contributing Member of the Eclipse Foundation, actively participating in the development of their robust ecosystem. By leveraging EF technologies, we offer innovative products and services that drive our corporate strategy forward. N3uron is Sparkplug Compatible Software.


CONTRIBUTING MEMBER
N3uron is a Contributing Member of the Eclipse Foundation, actively participating in the development of their robust ecosystem. By leveraging EF technologies, we offer innovative products and services that drive our corporate strategy forward. N3uron is Sparkplug Compatible Software.
FOLLOW US
N3uron Connectivity Systems • Paseo de la Castellana, 91, 4º, 1; Madrid, 28046, Spain • +34 911 841 938 • [email protected]
N3uron software is an Industrial Edge Platform for IIoT and DataOps that streamlines the flow of data between industrial systems and business applications, either on-premise or in the cloud. N3uron provides an out-of-the-box solution for data standardization, normalization and contextualization, seamless integration with industrial and IT systems, efficient information management, and unparalleled scalability and security. The N3uron platform makes it easier for operations teams to aggregate, manage and analyze industrial data, resulting in enhanced productivity and informed decision-making. Whether you're looking to optimize your operations, reduce downtime or improve product quality, the N3uron platform is the answer.
CONTRIBUTING MEMBER
N3uron is a Contributing Member of the Eclipse Foundation, actively participating in the development of their robust ecosystem. By leveraging EF technologies, we offer innovative products and services that drive our corporate strategy forward. N3uron is Sparkplug Compatible Software.


DLMS® UA MEMBER
N3uron is a member of the DLMS® User Association, the global community that drives standardization in the energy and water industry. Being part of the DLMS UA represents N3uron's commitment to advancing smart metering and energy management solutions.
FOLLOW US
N3uron Connectivity Systems • Paseo de la Castellana, 91, 4º, 1; Madrid, 28046, Spain • +34 911 841 938 • [email protected]